Optimizing Event Replay with Hybrid Snapshotting in Event-Sourced Systems
DOI:
https://doi.org/10.12928/biste.v8i2.14214Keywords:
Event Sourcing, State Reconstruction Latency, Hybrid Snapshotting, Distributed Event Stores, Recovery Time OptimizationAbstract
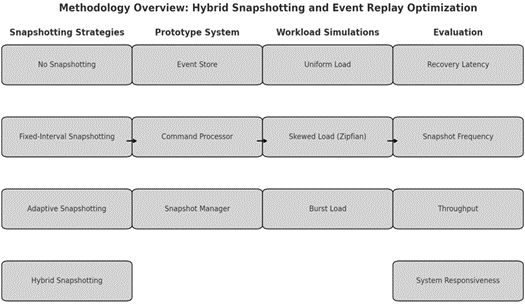
This study presents a hybrid framework for snapshotting and event replay optimization aimed at improving performance and scalability in event-sourced systems, where state reconstruction frequently experiences significant latency due to the replay of extensive event streams. Four snapshotting strategies were used to test this method: No Snapshotting, Fixed-Interval, Adaptive, and the new Hybrid method. The Adaptive strategy used dynamic triggers to make snapshots when an aggregate had more than 1,000 accesses in a five-minute window, when more than fifteen minutes had passed since the last snapshot, or when its event stream had more than 5,000 events. The Hybrid method used these adaptive triggers along with a fixed base interval of 5,000 events. For hot aggregates, the interval was cut in half to balance systematic coverage with runtime responsiveness. We built a prototype system in Java with Spring Boot and PostgreSQL. We used Kryo for snapshot serialization and Kafka to make controlled workloads. We ran tests on a 16-core Intel Xeon server to see how well it could handle event distributions that were uniform, skewed (Zipfian), or bursty, with anywhere from 10,000 to 1,000,000 events. We ran each configuration ten times and used 95% confidence intervals to find the average of the results. The results show that the Hybrid strategy consistently cut recovery latency, getting it down to 40 seconds under burst loads. This is a 58% improvement over Fixed-Interval and a 38% improvement over Adaptive. Throughput and responsiveness during normal operation were not affected, which is important. These results show that Hybrid snapshotting strikes a good balance between speed of recovery and storage overhead. This makes it a good choice for real-time, event-sourced applications. In the future, we will look into automatic tuning of snapshot intervals and adaptive thresholds, as well as adding support for distributed deployments and complex event schemas.
References
O. Jejić, M. Škembarević, and S. Babarogić, “Defining Software Architecture Modalities Based on Event Sourcing Architecture Pattern,” In European Conference on Advances in Databases and Information Systems, pp. 450-458, 2022, https://doi.org/10.1007/978-3-031-15743-1_41.
R. Manchana, “Event-Driven Architecture: Building Responsive and Scalable Systems for Modern Industries,” International Journal of Science and Research (IJSR), vol. 10, no. 1, pp. 1706-1716, 2021, https://doi.org/10.21275/SR24820051042.
O. C. Oyeniran, A. O. Adewusi, A. G. Adeleke, L. A. Akwawa, and C. F. Azubuko, “Microservices architecture in cloud-native applications: Design patterns and scalability,” Int. J. Adv. Res. Interdiscip. Sci. Endeavours, vol. 1, no. 2, pp. 92–106, 2024, https://doi.org/10.61359/11.2206-2409.
S. Akhmetzhanova, A. Serek, R. Kashayev, and A. Kozhamuratova, “Few-shot brain tumor classification: meta-vs metric-learning comparison,” Bulletin of Electrical Engineering and Informatics, vol. 14, no. 5, pp. 3913–3922, 2025, https://doi.org/10.11591/eei.v14i5.10706.
L. Zholshiyeva, T. Zhukabayeva, D. Baumuratova, and A. Serek, “Design of QazSL sign language recognition system for physically impaired individuals,” Journal of Robotics and Control (JRC), vol. 6, no. 1, pp. 191–201, 2025, https://doi.org/10.18196/jrc.v6i1.23879.
A. Serek, K. Orynbekova, A. Talasbek, D. Kariboz, G. Saimassay, and A. Bogdanchikov, “Recommendation system for human resource management by the use of Apache Spark cluster,” in Proc. 2023 17th Int. Conf. Electronics Computer and Computation (ICECCO), pp. 1–4, 2023, https://doi.org/10.1109/ICECCO58239.2023.10147129.
A. Serek, A. Issabek, A. Akhmetov, and A. Sattarbek, “Part-of-speech tagging of Kazakh text via LSTM network with a bidirectional modifier,” in Proc. 2021 16th Int. Conf. Electronics Computer and Computation (ICECCO), pp. 1–4, 2021, https://doi.org/10.1109/ICECCO53203.2021.9663794.
Y. Amirgaliyev, D. Kuanyshbay, and A. Shoiynbek, “Comparison of optimization algorithms of connectionist temporal classifier for speech recognition system,” Informatyka, Automatyka, Pomiary w Gospodarce i Ochronie Środowiska, vol. 9, 2019, https://doi.org/10.35784/iapgos.234.
D. N. Kuanyshbay, A. G. Serek, A. A. Shoiynbek, K. R. Sharipov, T. A. Shoiynbek, B. A. Meraliyev, and M. A. Meraliyev, “Development of an AI-Based Communication Fraud Detection System,” Appl. Math. Inf. Sci., vol. 19, no. 4, pp. 953–963, 2025, https://doi.org/10.18576/amis/190419.
M. Overeem, M. Spoor, S. Jansen, and S. Brinkkemper, “An empirical characterization of event sourced systems and their schema evolution—Lessons from industry,” J. Syst. Softw., vol. 178, p. 110970, 2021, https://doi.org/10.1016/j.jss.2021.110970.
J. Arafat, F. Tasmin, and S. Poudel, “Next-Generation Event-Driven Architectures: Performance, Scalability, and Intelligent Orchestration Across Messaging Frameworks,” arXiv preprint arXiv:2510.04404, 2025, https://doi.org/10.48550/arXiv.2510.04404.
M. Pantelelis and C. Kalloniatis, “Mapping CRUD to Events-Towards an object to event-sourcing framework,” In Proceedings of the 26th Pan-Hellenic Conference on Informatics, pp. 285-289, 2022, https://doi.org/10.1145/3575879.3576006.
M. V. S. Silva, L. F. C. dos Santos, M. S. Soares, and F. G. Rocha, “Guidelines for the Application of Event Driven Architecture in Micro Services with High Volume of Data,” In ICEIS (2), pp. 859-866, 2025, https://doi.org/10.5220/0013348600003929.
S. Lima, J. Correia, F. Araujo, and J. Cardoso, “Improving observability in event sourcing systems,” J. Syst. Softw., vol. 181, p. 111015, 2021, https://doi.org/10.1016/j.jss.2021.111015.
S. Lima, J. Correia, F. Araujo, and J. Cardoso, “Improving observability in event sourcing systems,” Journal of Systems and Software, vol. 181, p. 111015, 2021, https://doi.org/10.1016/j.jss.2021.111015.
A. Alhomssi and V. Leis, “Scalable and robust snapshot isolation for high-performance storage engines,” Proc. VLDB Endow., vol. 16, no. 6, pp. 1426–1438, 2023, https://doi.org/10.14778/3583140.3583157.
Z. Shen et al., “TierBase: A Workload-Driven Cost-Optimized Key-Value Store,” arXiv preprint arXiv:2505.06556, 2025, https://doi.org/10.1109/ICDE65448.2025.00049.
A. S. Krishnan and P. Schaumont, “Benchmarking and configuring security levels in intermittent computing,” ACM Transactions on Embedded Computing Systems (TECS), vol. 21, no. 4, pp. 1-22, 2022, https://doi.org/10.1145/3522748.
M. Moridi and W. Golab, "Snapshotting Mechanisms for Persistent Memory-Mapped Files," Proc. 2024 Workshop on Advanced Tools, Programming Languages, and Platforms for Implementing and Evaluating Algorithms for Distributed Systems, pp. 1–9, 2024, https://doi.org/10.1145/3663338.3665832.
P. Jayanti, S. Jayanti, and S. Jayanti, "MemSnap: A fast adaptive snapshot algorithm for RMWable shared-memory," Proc. 43rd ACM Symp. Principles of Distributed Computing, pp. 25–35, 2024, https://doi.org/10.1145/3662158.3662820.
F. Mohr, M. Wever, A. Tornede, and E. Hüllermeier, "Predicting machine learning pipeline runtimes in the context of automated machine learning," IEEE Trans. Pattern Anal. Mach. Intell., vol. 43, no. 9, pp. 3055–3066, 2021, https://doi.org/10.1109/TPAMI.2021.3056950.
Q. M. Rahman, P. Corke, and F. Dayoub, "Run-time monitoring of machine learning for robotic perception: A survey of emerging trends," IEEE Access, vol. 9, pp. 20067–20075, 2021, https://doi.org/10.1109/ACCESS.2021.3055015.
H. Naveed, "Runtime Monitoring of Human-Centric Requirements in Machine Learning Components: A Model-Driven Engineering Approach," in Proc. 2023 ACM/IEEE Int. Conf. Model Driven Eng. Lang. Syst. Companion (MODELS-C), pp. 146–152, 2023, https://doi.org/10.1109/MODELS-C59198.2023.00040.
A. Rahmatulloh, F. Nugraha, R. Gunawan and I. Darmawan, "Event-Driven Architecture to Improve Performance and Scalability in Microservices-Based Systems," 2022 International Conference Advancement in Data Science, E-learning and Information Systems (ICADEIS), pp. 01-06, 2022, https://doi.org/10.1109/ICADEIS56544.2022.10037390.
A. Serek, A. Issabek, and A. Bogdanchikov, "Distributed sentiment analysis of an agglutinative language via Spark by applying machine learning methods," in Proc. 2019 15th Int. Conf. Electronics, Computer and Computation (ICECCO), pp. 1–4, 2019, https://doi.org/10.1109/ICECCO48375.2019.9043264.
A. M. Dincă, S. D. Axinte, and I. C. Bacivarov, "In-memory versus on-disk databases: Best practices, use cases and architectural designs," in Proc. 2023 15th Int. Conf. Electronics, Computers and Artificial Intelligence (ECAI), pp. 1–6, 2023, https://doi.org/10.1109/ECAI58194.2023.10193891.
M. Alwadi, V. R. Kommareddy, C. Hughes, S. D. Hammond, and A. Awad, "Stealth-persist: Architectural support for persistent applications in hybrid memory systems," in Proc. 2021 IEEE Int. Symp. High-Performance Computer Architecture (HPCA), pp. 139–152, 2021, https://doi.org/10.1109/HPCA51647.2021.00022.
A. Hasnat and S. Akram, "SPIRIT: Scalable and Persistent In-Memory Indices for Real-Time Search," ACM Trans. Archit. Code Optim., vol. 22, no. 1, pp. 1–26, 2025, https://doi.org/10.1145/3703351.
M. Jangjou and M. K. Sohrabi, "A comprehensive survey on security challenges in different network layers in cloud computing," Arch. Comput. Methods Eng., vol. 29, no. 6, pp. 3587–3608, 2022, https://doi.org/10.1007/s11831-022-09708-9.
A. Serek and M. Zhaparov, "Optimizing preference satisfaction with genetic algorithm in matching students to supervisors," Appl. Math., vol. 18, no. 1, pp. 133–138, 2024, https://doi.org/10.18576/amis/180114.
S. Lee, A. Sharafat, I. S. Kim, and J. Seo, "Development and assessment of an intelligent compaction system for compaction quality monitoring, assurance, and management," Appl. Sci., vol. 12, no. 14, p. 6855, 2022, https://doi.org/10.3390/app12146855.
N. Park and S. Kim, “FlexSketch: Estimation of probability density for stationary and non-stationary data streams,” Sensors, vol. 21, no. 4, p. 1080, 2021, https://doi.org/10.3390/s21041080.
N. A. Khan, P. K. Jamwal, F. Hussain, M. H. Ghayesh, and S. Hussain, "Reinforcement Learning-Driven Path Generation for Ankle Rehabilitation Robot Using Musculoskeletal-Informed Energy Optimization," IEEE Trans. Neural Syst. Rehabil. Eng., 2025, https://doi.org/10.1109/TNSRE.2025.3566418.
O. C. Oyeniran, O. T. Modupe, A. A. Otitoola, O. O. Abiona, A. O. Adewusi, and O. J. Oladapo, "A comprehensive review of leveraging cloud-native technologies for scalability and resilience in software development," Int. J. Sci. Res. Arch., vol. 11, no. 2, pp. 330–337, 2024, https://doi.org/10.30574/ijsra.2024.11.2.0432.
A. Harika, P. Bhavani, P. Sriteja, S. Tajuddin and S. S. Harsha, "Optimizing Scalability and Resilience: Strategies for Aligning DevOps and Cloud-Native Approaches," 2023 3rd International Conference on Innovative Mechanisms for Industry Applications (ICIMIA), pp. 1161-1167, 2023, https://doi.org/10.1109/ICIMIA60377.2023.10426288.
A. Sutarman, J. Williams, D. Wilson, and F. B. Ismail, "A model-driven approach to developing scalable educational software for adaptive learning environments," Int. Trans. Educ. Technol. (ITEE), vol. 3, no. 1, pp. 9–16, 2024, https://doi.org/10.33050/itee.v3i1.663.
S. Balsam and D. Mishra, “Web application testing—Challenges and opportunities,” J. Syst. Softw., vol. 219, p. 112186, 2025, https://doi.org/10.1016/j.jss.2024.112186.
R. H. Kim, H. Song, and G. S. Park, “Moving real-time services to Web 3.0: Challenges and opportunities,” IEEE Trans. Serv. Comput., vol. 16, no. 6, pp. 4041–4059, 2023, https://doi.org/10.1109/TSC.2023.3307153.
Y. Zhang, M. M. A. Kabir, Y. Xiao, D. Yao and N. Meng, "Automatic Detection of Java Cryptographic API Misuses: Are We There Yet?," in IEEE Transactions on Software Engineering, vol. 49, no. 1, pp. 288-303, 2023, https://doi.org/10.1109/TSE.2022.3150302.
M. Moridi and W. Golab, “Snapshotting mechanisms for persistent memory-mapped files,” in Proc. 2024 Workshop on Advanced Tools, Programming Languages, and PLatforms for Implementing and Evaluating Algorithms for Distributed Systems, pp. 1–9, 2024, https://doi.org/10.1145/3663338.3665832.
B. Ding, W. Tong, Y. Hua, Z. Chen, X. Wei, and D. Feng, “Enabling reliable memory-mapped I/O with auto-snapshot for persistent memory systems,” IEEE Trans. Comput., 2024, https://doi.org/10.1109/TC.2024.3416683.
P. Royal, “Required Technologies,” in Building Modern Business Applications: Reactive Cloud Architecture for Java, Spring, and PostgreSQL, pp. 133–143, 2022, https://doi.org/10.1007/978-1-4842-8992-1_13.
K. C. Batchu, “Serverless ETL with Auto-Scaling Triggers: A Performance-Driven Design on AWS Lambda and Step Functions,” International Journal of Computer Technology and Electronics Communication, vol. 5, no. 3, pp. 5122-5131, 2022, https://doi.org/10.15680/IJCTECE.2022.0503004.
V. Cardellini, F. Lo Presti, M. Nardelli, and G. R. Russo, “Runtime adaptation of data stream processing systems: The state of the art,” ACM Computing Surveys, vol. 54, no. 11s, pp. 1-36, 2022, https://doi.org/10.1145/3514496.
D. Meißner, B. Erb, and F. Kargl, “Performance Engineering in Distributed Event-sourced Systems,” Distributed Event-Based Systems, pp. 242–245, 2018, https://doi.org/10.1145/3210284.3219770.
B. Erb, D. Meißner, G. Habiger, J. Pietron, and F. Kargl, “Consistent retrospective snapshots in distributed event-sourced systems,” pp. 1–8, 2017, https://doi.org/10.1109/NetSys.2017.7903947.
R. Malyi and P. Serdyuk, “Developing a performance evaluation benchmark for event sourcing databases,” Information Systems and Networks, no. 15, pp. 159-167, 2024, https://doi.org/10.23939/sisn2024.15.159.
K. R. Thondalapally, “Event-Driven Architectures: The Foundation of Modern Distributed Systems,” IJSAT-International Journal on Science and Technology, vol. 16, no. 1, 2025, https://doi.org/10.71097/IJSAT.v16.i1.2907.
P. Bali, L. S. Kutikuppala, P. Avti, and B. Medhi, "Data fraud and essence of data verifiability," in Quality Assurance Implementation in Research Labs, pp. 137–159, 2021, https://doi.org/10.1007/978-981-16-3074-3_9.
A. A. Khan et al., “BAIoT-EMS: Consortium network for small-medium enterprises management system with blockchain and augmented intelligence of things,” Engineering Applications of Artificial Intelligence, vol. 141, p. 109838, 2025, https://doi.org/10.1016/j.engappai.2024.109838.
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Akhulbay Shyngys, Azamat Serek, Darkhan Kuanyshbay

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Authors who publish with this journal agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work (See The Effect of Open Access).
This journal is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.