Implementation of Vehicle Ad Hoc Networks for TPBFT on Latency and Fault Tolerance in Blockchain Systems
DOI:
https://doi.org/10.12928/biste.v8i2.15227Keywords:
VANET, TPBFT, Latency, Throughput, BlockchainAbstract
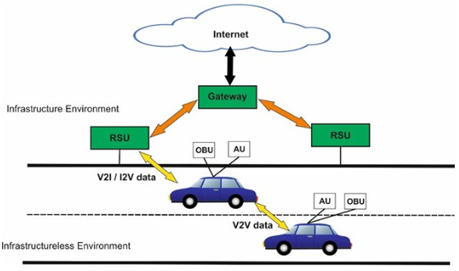
In this paper, examines the combination of Vehicle Ad hoc Networks (VANETs) and a new consensus mechanism called Trust Practical Byzantine Fault Tolerance (TPBFT) that is aimed at improving latency and fault tolerance of decentralized vehicular networks. The VANETs are described by dynamic topology and mobile node and pose special security as well as reliability issues especially in scalable networks. The conventional Byzantine Fault Tolerance (BFT) protocols are ineffective because they incur communication overhead and scaling problems. This paper suggests TPBFT as a powerful consensus mechanism that is suitable to use in vehicular networks and is effective even when malicious or malfunctioning nodes are involved. To model real-life traffic patterns and communication scenarios, the research methodology presupposes extensive simulations based on Simulation of Urban Mobility (SUMO) tool and real-world Open Street Map (OSM) data with the help of the Python program. The performance of TPBFT is strictly tested and compared to the classic Practical Byzantine Fault Tolerance (PBFT) protocol through the analysis of the consensus latency, system throughput, and fault tolerance resilience. The findings indicate TPBFT has a shorter consensus latency (16 to 28 ms) and a greater throughput compared to PBFT and was more effective in time-constrained vehicular usage. The present work makes TPBFT an effective decentralized mechanism that allows achieving low latency, high throughput, and high resistance to Byzantine failures, offering a safe platform to deploy the blockchain technology in smart transportation systems. The optimization of the energy consumption profile of network nodes, as well as the refinement of the consensus process on the application of blockchain-based VANET architecture into practice, will be the subject of future research.
References
P. Sapkale, S. Mehta, and S. Balamurugan, Quantum Computing and Machine Learning for 6G. John Wiley & Sons. 2026, https://doi.org/10.1002/9781394238118.
G. Singh, S. Sharma, A. K. J. Saudagar, and S. Kumar, "A secure group-based authentication protocol for IoVT in 5G-enabled smart transportation and road safety systems," Scientific Reports, 2026, https://doi.org/10.1038/s41598-025-31123-w.
T. D. Nguyen, N. A. Tong, B. P. Nguyen, Q. V. Hung Nguyen, P. L. Nguyen and T. T. Huynh, "Hierarchical Federated Learning in MEC Networks with Knowledge Distillation," 2024 International Joint Conference on Neural Networks (IJCNN), pp. 1-8, 2024, https://doi.org/10.1109/IJCNN60899.2024.10651323.
L. Qudus, "Resilient systems: building secure cyber-physical infrastructure for critical industries against emerging threats," Int J Res Publ Rev, vol. 6, no. 1, pp. 3330-46, 2025, https://doi.org/10.55248/gengpi.6.0125.0514.
N. Canino, P. Dini, S. Mazzetti, D. Rossi, S. Saponara, and E. Soldaini, “Cybersecurity of automotive wired networking systems: evolution, challenges, and countermeasures,” Electronics, vol. 14, no. 3, p. 471, 2025, https://doi.org/10.3390/electronics14030471.
M. AlMarshoud, M. Sabir Kiraz, and A. H. Al-Bayatti, "Security, privacy, and decentralized trust management in VANETs: A review of current research and future directions," ACM Computing Surveys, vol. 56, no. 10, pp. 1-39, 2024, https://doi.org/10.1145/3656166.
R. Sarpong, F. Araújo, and B. Sousa, "The potential of SDNs and multihoming in VANETs: A Comprehensive Survey," in 2025 12th International Conference on Future Internet of Things and Cloud (FiCloud), pp. 265-272, 2025, https://doi.org/10.1109/FiCloud66139.2025.00043.
A. J. Albarakati, "Blockchain-Based Trust Management Framework Using Spiking Neural Networks for 6G-Enabled IoT Ecosystems: A Secure Approach for Intelligent Transportation Systems," Journal of Circuits, Systems and Computers, p. 2642010, 2026, https://doi.org/10.1142/S0218126626420107.
Z. Ullah et al., "TrustChain‐VANETs: Blockchain and IPFS Integration for Reliable and Secure Vehicular Communication in Intelligent Transportation Systems (ITS)," IET Intelligent Transport Systems, vol. 19, no. 1, p. e70051, 2025, https://doi.org/10.1049/itr2.70051.
A. Fujihara, "Exploring the universality of finality time in proof-of-stake blockchains: empirical analysis and mathematical formulation of size-synchrony antagonism," in 2025 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), pp. 1-5, 2025, https://doi.org/10.1109/ICBC64466.2025.11114702.
Y. Xu, Y. Lei, L. Tang, X. Li, and Z. Sun, "A Hybrid Consensus Optimization Algorithm for Blockchain in Supply Chain Traceability," Electronics, vol. 15, no. 1, p. 77, 2025, https://doi.org/10.3390/electronics15010077.
S. Khokha, “Integrating safety and security in autonomous vehicles: a comprehensive review,” In 2024 4th International Conference on Sustainable Expert Systems (ICSES), pp. 460-464 2024, https://doi.org/10.1109/ICSES63445.2024.10763275.
N. Dasanayaka, K. F. Hasan, C. Wang, and Y. Feng, “Enhancing vulnerable road user safety: A survey of existing practices and consideration for using mobile devices for V2X connections,” arXiv preprint arXiv:2010.15502, 2020, https://doi.org/10.48550/arXiv.2010.15502.
T. Alladi, V. Chamola, N. Sahu, V. Venkatesh, A. Goyal, and M. Guizani, "A comprehensive survey on the applications of blockchain for securing vehicular networks," IEEE Communications Surveys & Tutorials, vol. 24, no. 2, pp. 1212-1239, 2022, https://doi.org/10.1109/COMST.2022.3160925.
X. Li, W. Jiang, W. Wang, T. Zhou, K. Wang, and S. Liu, "Joint channel connectivity and interference management in DT-assisted cognitive vehicular networks," Ad Hoc Networks, vol. 183, p. 104094, 2026, https://doi.org/10.1016/j.adhoc.2025.104094.
A. Gheysari and H. R. Zarandi, "Security-aware optimization of PoW-based blockchain performance using a genetic algorithm approach," Sustainable Computing: Informatics and Systems, p. 101232, 2025, https://doi.org/10.1016/j.suscom.2025.101232.
D. Jia, G. Yang, M. Huang, J. Xin, G. Wang, and G. Y. Yuan, "An efficient privacy-preserving blockchain storage method for internet of things environment," World Wide Web, pp. 1-18, 2023, https://doi.org/10.1007/s11280-023-01172-0.
S. Tang, Z. Wang, J. Jiang, S. Ge, and G. Tan, "Improved PBFT algorithm for high-frequency trading scenarios of alliance blockchain," Scientific Reports, vol. 12, no. 1, p. 4426, 2022, https://doi.org/10.1038/s41598-022-08587-1.
S. B. A. Bukhari, H. Albalawi, A. Wadood, and A. M. Alatwi, "Deep learning-driven fault detection and classification in microgrids using Temporal Convolutional Network," Computers and Electrical Engineering, vol. 129, p. 110777, 2026, https://doi.org/10.1016/j.compeleceng.2025.110777.
A. Behura, A. Kumar, and P. K. Jain, “A comparative performance analysis of vehicular routing protocols in intelligent transportation systems,” Telecommunication Systems, vol. 88, no. 1, p. 26, 2025, https://doi.org/10.1007/s11235-024-01243-1.
H. Wu, C. Yue, L. Zhang, Y. Li, and M. A. Imran, "When Distributed Consensus Meets Wireless Connected Autonomous Systems: A Review and A DAG-based Approach," IEEE Network, vol. 39, no. 1, pp. 261-269 2024, https://doi.org/10.1109/MNET.2024.3482273.
O. B. Akinola, "Comparative Insights On The Legal Status Of Cryptocurrencies: Lessons For Uganda," The Nnamdi Azikiwe University Journal of Commercial and Property Law, vol. 13, no. 1, 2026, https://journals.ezenwaohaetorc.org/index.php/NAUJCPL/article/view/3593.
J. K. Adeniyi et al., "A biometrics-generated private/public key cryptography for a blockchain-based e-voting system," Egyptian Informatics Journal, vol. 25, 2024, https://doi.org/10.1016/j.eij.2024.100447.
C. Delgado-von-Eitzen, M. J. Fernández-Iglesias, L. Anido-Rifón, and F. A. Mikic-Fonte, "Blockchain beyond immutability: Application firewalls on ethereum-based platforms," Computer Standards & Interfaces, vol. 95, p. 104038, 2026, https://doi.org/10.1016/j.csi.2025.104038.
M. A. Shawky et al., "Blockchain-based secret key extraction for efficient and secure authentication in VANETs," Journal of Information Security and Applications, vol. 74, p. 103476, 2023, https://doi.org/10.1016/j.jisa.2023.103476.
Y. Xie, C. Tang, Z. Chen, J. Lai, Z. Zheng, and X. Yu, "Towards proof-of-prospect consensus mechanism for maximizing consumers’ satisfaction in distributed energy systems," Science China Information Sciences, vol. 69, no. 2, p. 122202, 2026, https://doi.org/10.1007/s11432-024-4438-5.
A. Dutta, L. M. Samaniego Campoverde, M. Tropea, and F. De Rango, "A comprehensive review of recent developments in vanet for traffic, safety & remote monitoring applications," Journal of Network and Systems Management, vol. 32, no. 4, p. 73, 2024, https://doi.org/10.1007/s10922-024-09853-5.
V. Alagappan, "A Governance Model for IoT Data in Global Manufacturing," arXiv preprint arXiv:2601.09744, 2026, https://doi.org/10.48550/arXiv.2601.09744.
M. G. Xevgenis, M. Polychronaki, D. G. Kogias, H. C. Leligkou, and E. Liotou, "Securing Zero-Touch Networks with Blockchain: Decentralized Identity Management and Oracle-Assisted Monitoring," Electronics, vol. 15, no. 2, p. 266, 2026, https://doi.org/10.3390/electronics15020266.
P. Selvaprabhu, "An examination of distributed and decentralized systems for trustworthy control of supply chains," IEEE access, vol. 11, pp. 137025-137052, 2023, https://doi.org/10.1109/ACCESS.2023.3338739.
M. Stephens, "Enhancing Global Cybersecurity Resilience: Navigating the Subconscious Fallacies within Critical Infrastructure Protection," Journal of Information Warfare, vol. 23, no. 3, pp. 82-94, 2024, https://doi.org/10.34190/eccws.23.1.2213.
K. Sharma, K. Bhatt, and I. Giri, “Regulatory Migration to Europe: ICO Reallocation Following US Securities Enforcement,” arXiv preprint arXiv:2602.00138, 2026, https://doi.org/10.48550/arXiv.2602.00138.
N. S. Liqaa Saadi Mezher, Dheyaa Jasim Kadhim, "Load Balancing Based Intelligent Software Defined Networking (SDN) Controller," Journal of Information Systems Engineering and Management, vol. 10, no. 1, pp. 57 - 68, 2025, https://doi.org/10.52783/jisem.v10i1s.101.
N. M. Nasir, S. Hassan and K. Mohd Zaini, "Securing Permissioned Blockchain-Based Systems: An Analysis on the Significance of Consensus Mechanisms," in IEEE Access, vol. 12, pp. 138211-138238, 2024, https://doi.org/10.1109/ACCESS.2024.3465869.
K. W. Lin, Y.-J. Zheng, J.-C. Chen, W.-C. Wang, and C.-C. Chen, "A parallel and distributed C4. 5 algorithm in cloud computing environments," Computing, vol. 107, no. 2, pp. 1-38, 2025, https://doi.org/10.1007/s00607-025-01415-0.
J. A. R. de Souza, E. R. Cavalcanti, T. de Sales Bezerra, and R. C. d. M. Gomes, "VANETs’ research overview updated: past, present and future," Journal of the Brazilian Computer Society, vol. 30, no. 1, pp. 380-393, 2024, https://doi.org/10.5753/jbcs.2024.3354.
L. S. Mezher, "An Overview on Vehicular Ad Hoc Networks Security," Journal of Engineering Research and Reports, vol. 28, no. 1, pp. 189-204, 2026, https://doi.org/10.9734/jerr/2026/v28i11769.
R. Wang et al., "Parallel Byzantine fault tolerance consensus based on trusted execution environments," Peer-to-Peer Networking and Applications, vol. 18, no. 1, p. 31, 2025, https://doi.org/10.1007/s12083-024-01830-8.
B. L. Nguyen, D. T. Ngo, and H. L. Vu, “Vehicle Communications for Infotainment Applications,” In Handbook of Real-Time Computing, pp. 705-722, 2022, https://doi.org/10.1007/978-981-287-251-7_44.
L. S. Mezher and M. H. Saleh, "Enhancing VANET Security using Blockchain and SHA3-256 in Python," Journal of Studies in Science and Engineering, vol. 5, no. 1, pp. 84-109, 2025, https://doi.org/10.53898/josse2025515.
J. Ghosh, N. Kumar, K. A. Al-Utaibi, S. M. Sait, V. N. Vo, and C. So-In, "Reliable data transmission for a VANET-IoIT architecture: A DNN approach," Internet of Things, vol. 25, p. 101129, 2024, https://doi.org/10.1016/j.iot.2024.101129.
N. Wang et al., "Application of the BCT Model Based on Process and Behavioral Interventions to Improve the Quality of Blood Culture Collection," Infection Prevention in Practice, p. 100509, 2026, https://doi.org/10.1016/j.infpip.2026.100509.
E. Ngatunga, M. Kissaka, and A. T. Abdalla, "Performance evaluation of cluster-based schemes for message dissemination in a vehicle-to-vehicle communication in urban environment," Cogent Engineering, vol. 11, no. 1, p. 2348885, 2024, https://doi.org/10.1080/23311916.2024.2348885.
M. Soori, F. K. G. Jough, R. Dastres, and B. Arezoo, "Blockchains for industrial Internet of Things in sustainable supply chain management of industry 4.0, a review," Sustainable Manufacturing and Service Economics, vol. 3, p. 100026, 2024, https://doi.org/10.1016/j.smse.2024.100026.
A. Kumar, L. Vishwakarma, and D. Das, "R-PBFT: A secure and intelligent consensus algorithm for Internet of vehicles," Vehicular Communications, vol. 41, p. 100609, 2023, https://doi.org/10.1016/j.vehcom.2023.100609.
A. Alshahrani et al., "An Intelligent Latency Aware DDoS Detection Framework for Secure Vehicular Ad Hoc Networks," Transactions on Emerging Telecommunications Technologies, vol. 37, no. 1, p. e70348, 2026, https://doi.org/10.1002/ett.70348.
S. BK and F. Azam, "Ensuring security and privacy in vanet: A comprehensive survey of authentication approaches," Journal of Computer Networks and Communications, vol. 2024, no. 1, p. 1818079, 2024, https://doi.org/10.1155/2024/1818079.
O. Q. Wu, R. Kapuscinski, and S. Suresh, "On the distributed energy storage investment and operations," Manufacturing & Service Operations Management, vol. 25, no. 6, pp. 2277-2297, 2023, https://doi.org/10.1287/msom.2020.0652.
S. Mondal, K. Dogra, S. Gupta, and S. K. Gupta, "A Blockchain‐Based OBD Architecture for Secure Data Sharing in Smart Vehicle Ecosystems," Security and Privacy, vol. 9, no. 1, p. e70158, 2026, https://doi.org/10.1002/spy2.70158.
A. Shahidinejad, J. Abawajy, and S. Huda, "Anonymous lattice-based authentication protocol for vehicular communications," Vehicular Communications, vol. 48, 2024, doi: 10.1016/j.vehcom.2024.100803, https://doi.org/10.1016/j.vehcom.2024.100803.
J. A. Alzubi, N. R. Lavuri, K. Dharavath, N. Nallameti, S. Venugopal, and P. Palanisamy, "A Secure Authentication and Task Offloading Model Using Blockchain‐Assisted Hybrid Serial Learning in Multiaccess Edge Computing for Vehicular Ad Hoc Networks Sector," International Journal of Communication Systems, vol. 39, no. 3, p. e70382, 2026, https://doi.org/10.1002/dac.70382.
R. Bala, R. Manoharan, and G. Ramya, "Trust models for blockchain networks: a comprehensive review," Journal of Ambient Intelligence and Humanized Computing, pp. 1-20, 2026, https://doi.org/10.1007/s12652-025-05027-6.
J. Grover, “Security of Vehicular Ad Hoc Networks using blockchain: A comprehensive review,” Vehicular Communications, vol. 34, p. 100458, 2022, https://doi.org/10.1016/j.vehcom.2022.100458.
A. A. Al-awamy, N. Al-shaibany, A. Sikora, and D. Welte, "Hybrid Consensus Mechanisms in Blockchain: A Comprehensive Review," International Journal of Intelligent Systems, vol. 2025, no. 1, p. 5821997, 2025, https://doi.org/10.1155/int/5821997.
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Liqaa Saadi Mezher, Ayam Mohsen Abbass, Muna Hadi Saleh

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Authors who publish with this journal agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work (See The Effect of Open Access).
This journal is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.