Optimization of real-time forest monitoring system using yolo v9 object detection and 2.4 ghz wireless network: resource allocation, energy efficiency, and industrial deployment strategies
DOI:
https://doi.org/10.12928/ijio.v7i1.11899Keywords:
Energy optimization, Forest monitoring, Industrial, Wireless Sensor Networks, YOLO Object DetectionAbstract
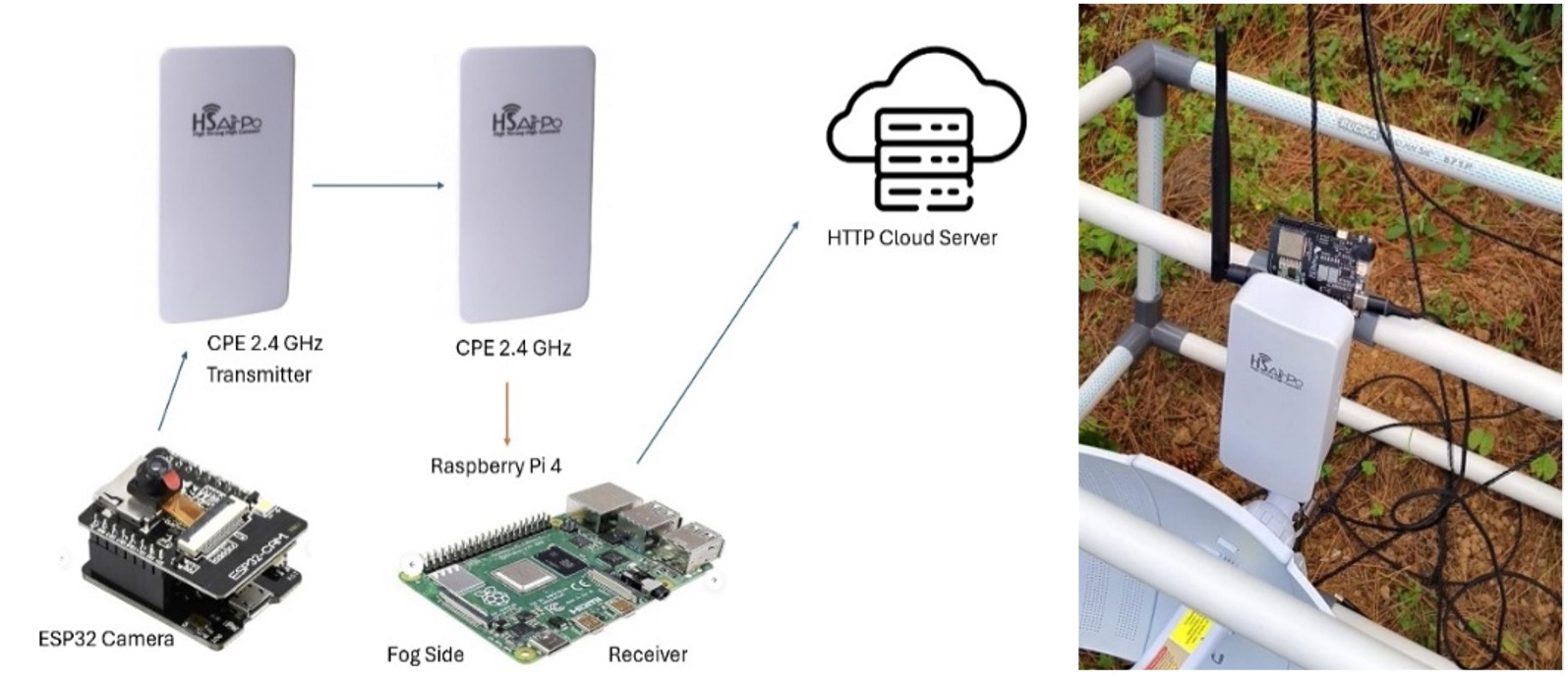
Large forest areas are increasingly exposed to illegal activities and environmental threats, while conventional monitoring systems suffer from limited coverage, high energy consumption, and delayed response. To address these challenges, this study proposes an optimized real-time forest monitoring system designed for industrial-scale deployment in remote environments. The primary objective is to enhance surveillance efficiency by integrating AI-based object detection, long-range wireless communication, and resource-efficient system design. The proposed system employs ESP32-CAM sensor nodes integrated with 2.4 GHz CPE wireless links and a gateway-based YOLOv9 object detection framework. Bandwidth utilization is optimized through selective transmission of processed detection metadata instead of raw images, while deployment parameters are optimized using simulation-based planning. A web-based monitoring platform with an optimized REST API supports real-time visualization and alert generation. Experimental results show that the system achieves reliable communication up to 500 m with packet loss below 5% and latency under 50 ms at distances up to 300 m. Human detection accuracy reaches 98.5% under optimal conditions, with performance degradation observed in dense vegetation and low-light environments. Energy evaluation confirms sustainable operation, with ESP32 nodes consuming 160 mA and the gateway operating at 3.7 W. Comparative analysis indicates reductions of 37% in deployment cost, 24% in energy consumption, and 51% in latency compared to similar systems. This study concludes that the proposed architecture effectively balances accuracy, scalability, cost, and energy efficiency. The novelty lies in the integrated optimization of edge-based AI detection, selective data transmission, and simulation-driven deployment for industrial forest monitoring.
References
J. Terven, D. M. Córdova-Esparza, and J. A. Romero-Gonzalez, “A comprehensive review of yolo architectures in computer vision: From yolov1 to yolov8 and yolo-nas,” Machine learning Know. Extr. mdpi.com, 2023, [Online]. Available: https://doi.org/10.3390/make5040083.
M. Bera, S. Das, S. Garai, S. Dutta, M. R. Choudhury, and G. Chatterjee, “Advancing energy efficiency: innovative technologies and strategic measures for achieving net zero emissions,” Carbon Footprints, 2025, [Online]. Available: http://dx.doi.org/10.20517/cf.2024.48.
C. Gupta, N. S. Gill, P. Gulia, A. Kumar, H. Karamti, and D. M. Moges, “An optimized YOLO NAS based framework for realtime object detection,” Scientific reports. nature.com, 2025, [Online]. Available: https://doi.org/10.1038/s41598-025-17919-w.
E. Sengun, S. Aksoy, E. Sertel, and J. E. S. Fransson, “Comparative Analysis of YOLOv8 and YOLOv11 on Tree Detection Using UAV RGB and Laser Scanning Data,” ISPRS Ann., 2025, [Online]. Available: https://doi.org/10.5194/isprs-annals-X-2-W2-2025-173-2025.
R. A. Dwiyanto, G. A. Mutiara, and M. I. Sari, “Performance analysis of REST API in a real-time IoT-based vehicle monitoring system,” Int J Reconfigurable & Embedded Systems, 2025, [Online]. Available: http://doi.org/10.11591/ijres.v14.i3.pp766-784.
M. N. Alatawi, “Optimizing security and energy efficiency in IoT-Based health monitoring systems for wireless body area networks,” Scientific Reports, 2025, [Online]. Available: https://doi.org/10.1038/s41598-025-11253-x.
C. L. Kok, J. B. Heng, Y. Y. Koh, and T. H. Teo, “Energy-, cost-, and resource-efficient IoT hazard detection system with adaptive monitoring,” Sensors, 2025, [Online]. Available: https://doi.org/10.3390/s25061761.
V. Abilasha and A. Karthikeyan, “IEEE 802.11 af-enabled scalable cognitive radio sensor networks with adaptive priority management for early forest fire forewarning,” Scientific Reports, 2025, [Online]. Available: https://doi.org/10.1038/s41598-025-21050-1.
S. Dolhopolov, T. Honcharenko, D. Chernyshev, and V. Hots, “YOLOv5-based Object Detection for Construction Site Efficiency: Equipment, Tool, and Vehicle Recognition.,” ITTAP. ceur-ws.org, 2024, [Online]. Available: https://ceur-ws.org/Vol-3896/paper4.pdf.
J. S. Manoharan, G. Vijayasekaran, I. Gugan, and P. N. Priyadharshini, “Adaptive forest fire optimization algorithm for enhanced energy efficiency and scalability in wireless sensor networks,” Ain Shams Engineering Journal, 2025. Available: https://doi.org/10.1016/j.asej.2025.103406.
S. Tahcfulloh, D. Maulianawati, and D. Wiharyanto, “Optimizing 2.4 GHz Wireless Networks in Shrimp Ponds with Particle Swarm Optimization,” Jurnal Ilmiah Teknik Elektro Komputer dan Informatika, 2024, [Online]. Available: https://doi.org/10.26555/jiteki.v10i4.30236
J. Logeshwaran and N. Shanmugasundaram, “Energy‐efficient resource allocation model for device‐to‐device communication in 5G wireless personal area networks,” Int. J. of Communication Systems, 2023, doi: 10.1002/dac.5524.
R. K. POLAGANGA and S. Marupaduga, “System and method for optimizing use of wireless communication protocols,” US Pat. 11,979,777, 2024, [Online]. Available: https://patents.google.com/patent/US11979777B2/en.
L. Shanmugam, S. Jangoan, and K. K. Sharma, “Dynamic resource allocation in edge computing for ai/ml applications: Architectural framework and optimization techniques,” J. Knowl. Learn. and Science Technology, 2023, [Online]. Available: https://doi.org/10.60087/jklst.vol2.n2.p397.
F. Manzi, E. Tuyishime, A. Hitayezu, and M. Gedeon, “Leveraging Machine Learning and Raspberry Pi for Enhanced Wildlife Remote Monitoring and Localization,” Software Engineering Methods in Syst. Softw., 2023, doi: 10.1007/978-3-031-53549-9_39.
K. V Reddy, B. S. K. Reddy, V. Goutham, M. Mahesh, and J. S. Nisha, “Edge AI in sustainable farming: Deep learning-driven IoT framework to safeguard crops from wildlife threats,” IEEE, 2024. Available: https://ieeexplore.ieee.org/abstract/document/10540092/.
S. Sarvaiya, S. Ganesh, and B. Xu, “Comparative analysis of hybrid vehicle energy management strategies with optimization of fuel economy and battery life,” Energy, 2021, [Online]. Available: https://www.sciencedirect.com/science/article/pii/S0360544221008537.
V. Panchal, “Designing for Longer Battery Life: Power Optimization Strategies in Modern Mobile SOCS,” International Journal of Electrical Engineering and & Technology, 2025, [Online]. Available: https://doi.org/10.34218/IJEET_16_01_001.
B. Zhao, “Deep learning for environmental sound classification,” IEEE Transactions on Audio, Speech, and Language. 2020.
I. Dawar, S. D. Gupta, R. Singh, Y. Kothari, and S. Layek, “Forest fire detection using deep learning techniques,” 2023 2nd International Conference on Vision Towards Emerging Trends in Communication and Networking Technologies (ViTECoN), 2023, [Online]. Available: https://doi.org/10.1109/ViTECoN58111.2023.10157262.
Y. Basanthi, K. Kalaiselvi, and V. S. Murugan, “Integrated Engroove Leach Clustering protocol with Artificial Bee Colony Optimization for Energy Efficient Routing in WSN,” 2024 4th International Conference on Soft Computing for Security Applications (ICSCSA), 2024, [Online]. Available: https://doi.org/10.1109/ICSCSA64454.2024.00101.
N. Meenakshi, S. Ahmad, A. V Prabu, and H. A. M. Abdeljaber, “Efficient communication in wireless sensor networks using optimized energy efficient engroove leach clustering protocol,” Tsinghua Sci. and technology, 2024, [Online]. Available: https://doi.org/10.26599/TST.2023.9010056.
Y. Yang, “Blockchain-Enabled Multiparty Computation for Privacy Preserving and Public Audit in Industrial IoT,” IEEE Trans. Ind. Informatics, vol. 18, no. 12, pp. 9259–9267, 2022, doi: 10.1109/TII.2022.3177630.
A. Sharma, T. Bhatia, R. K. Singh, and A. Sharma, “Developing the framework of blockchain-enabled agri-food supply chain,” Bus. Process Manag. J., vol. 30, no. 1, pp. 291–316, Feb. 2024, doi: 10.1108/BPMJ-01-2023-0035.
W. Zhang, “TIIA: A blockchain-enabled Threat Intelligence Integrity Audit scheme for IIoT,” Futur. Gener. Comput. Syst., vol. 132, pp. 254–265, 2022, doi: 10.1016/j.future.2022.02.023.
R. Martínez-Peláez, A. Ochoa-Brust, S. Rivera, V. G. Félix, and L. J. Mena, “Role of digital transformation for achieving sustainability: mediated role of stakeholders, key capabilities, and technology,” Sustainability, 2023, [Online]. Available: https://doi.org/10.3390/su151411221.
D. Magrin, “Performance Evaluation of 802.11ax OFDMA Through Theoretical Analysis and Simulations,” IEEE Trans. Wirel. Commun., vol. 22, no. 8, pp. 5070–5083, 2023, doi: 10.1109/TWC.2022.3231447.
V. S. Gadakh, “Application of complex proportional assessment method for vendor selection,” Int. J. Logist. Res. Appl., vol. 17, no. 1, pp. 23–34, Jan. 2014, doi: 10.1080/13675567.2013.836159.
A. Duch and C. Martinez, “Improving the Performance of Multidimensional Search Using Fingers,” ACM J. Exp. Algorithmics, vol. 10, p. 2.4, 2005, doi: 10.1145/1064546.1180615.
M. O. Tarar, “Accurate prediction of remaining useful life for lithium-ion battery using deep neural networks with memory features,” Front. Energy Res., vol. 11, 2023, doi: 10.3389/fenrg.2023.1059701.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Rachmad Andri Atmoko, Rifqi Rahmat Hidayatullah, Septian Ghuslal Nur Na’im, Akas Bagus Setiawan

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
License and Copyright Agreement
In submitting the manuscript to the journal, the authors certify that:
- They are authorized by their co-authors to enter into these arrangements.
- The work described has not been formally published before, except in the form of an abstract or as part of a published lecture, review, thesis, or overlay journal. Please also carefully read the International Journal of Industrial Optimization (IJIO) Author Guidelines at http://journal2.uad.ac.id/index.php/ijio/about/submissions#onlineSubmissions
- That it is not under consideration for publication elsewhere,
- That its publication has been approved by all the author(s) and by the responsible authorities tacitly or explicitly of the institutes where the work has been carried out.
- They secure the right to reproduce any material that has already been published or copyrighted elsewhere.
- They agree to the following license and copyright agreement.
Copyright
Authors who publish with the International Journal of Industrial Optimization (IJIO) agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License (CC BY-SA 4.0) that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work.

1.png)