Intruder Detection Systems on Computer Networks Using Host Based Intrusion Detection System Techniques
DOI:
https://doi.org/10.12928/biste.v3i1.1752Keywords:
IDS, Snort, HIDS, DOS, DDOS, Keamanan Jaringan KomputerAbstract
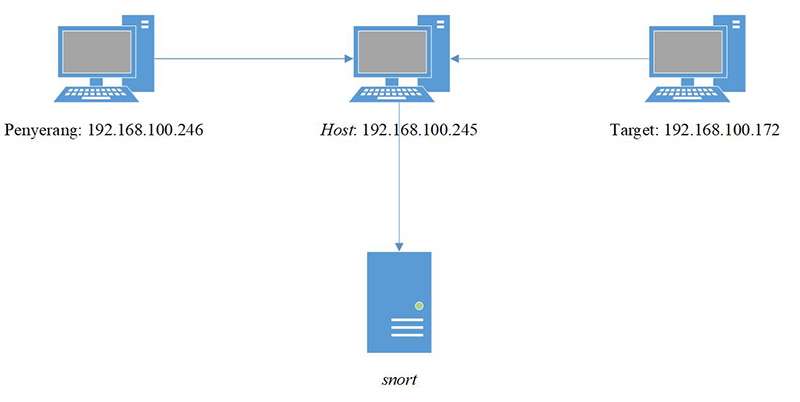
The openness of access to information raises various problems, including maintaining the validity and integrity of data, so a network security system is needed that can deal with potential threats that can occur quickly and accurately by utilizing an IDS (intrusion detection system). One of the IDS tools that are often used is Snort which works in real-time to monitor and detect the ongoing network by providing warnings and information on potential threats in the form of DoS attacks. DoS attacks run to exhaust the packet path by requesting packets to a target in large and continuous ways which results in increased usage of CPU (central processing unit), memory, and ethernet or WiFi networks. The snort IDS implementation can help provide accurate information on network security that you want to monitor because every communication that takes place in a network, every event that occurs and potential attacks that can paralyze the internet network are monitored by snort.References
F. N. R. Muh. Husain, A. I.M Akasara, “Implementasi Keamanan Server Pada Jaringan Wireless Menggunakan Metode Intrusion Detection and Prevention System (Idps) (Studi Kasus : Techno’S Studio),” semanTIK, vol. 4, no. 2, pp. 11–20, 2018, DOI: https://doi.org/10.5281/zenodo.1407864
D. A. Nugroho, A. F. Rochim, and E. D. Widianto, “Perancangan dan Implementasi Instrusion Detection System di Jaringan Universitas Diponegoro,” J. Teknol. dan Sist. Komput., vol. 3, no. 2, p. 171, 2015. DOI: https://doi.org/10.14710/jtsiskom.3.2.2015.171-178
M. Affandi and S. Setyowibowo, “Implementasi Snort Sebagai Alat Pendeteksi Intrusi Menggunakan Linux,” J. Teknol. Inf., vol. 4, no. 2, 2013. Online
W. Fathoni, Fitriyani, and G. N. Nurkahfi, “Deteksi Penyusupan Pada Jaringan Komputer Menggunakan Ids Snort,” e-Proceeding Eng., vol. 3, no. 1, pp. 1169–1172, 2016. Online
I. A. Sobari, “Rancangan Wireless Intrusion Detection System Menggunakan Snort,” J. Techno Nusa Mandiri, vol. 12, no. 1, pp. 1–9, 2015. Online
A. P. Wicaksono, J. Raya, D. Po, and B. Purwokerto, “Sistem Deteksi Intrusi dengan Snort (Intrusion Detection System with Snort),” JUITA - J. Inform., vol. 3, no. 1, pp. 31–34, 2014, doi: https://doi.org/10.30595/juita.v3i1.850
E. K. Dewi, “Analisis Log Snort Menggunakan Network Forensic,” JIPI (Jurnal Ilm. Penelit. dan Pembelajaran Inform., vol. 2, no. 2, pp. 72–79, 2017, doi: https://doi.org/10.29100/jipi.v2i2.370
N. Sahrun, R. Roestam, and D. Sarjon, “Pengembangan Sistem Keamanan Jaringan Komputer Melalui Perumusan Aturan (Rule) Snort untuk Mencegah Serangan Synflood,” SATIN - Sains dan Teknol. Inf., vol. 1, no. 2, pp. 25–31, 2015. Online
R. Hermawan, “Analisis Konsep Dan Cara Kerja Serangan Komputer Distributed Denial of Service (Ddos),” Fakt. Exacta, vol. 5, no. 1, pp. 1–14, 2013. Online
A. Fadlil, I. Riadi, and S. Aji, “Review of detection DDOS attack detection using naive bayes classifier for network forensics,” Bull. Electr. Eng. Informatics, vol. 6, no. 2, pp. 140–148, 2017, doi: https://doi.org/10.11591/eei.v6i2.605
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2021 Rio Widodo, Imam Riadi

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Authors who publish with this journal agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work (See The Effect of Open Access).
This journal is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.