Hybird Autokey Cipher Algorithm Implementation Reverse Key and Standard Data Encryption for App-Based Text Messages
DOI:
https://doi.org/10.12928/mf.v5i2.8451Abstract
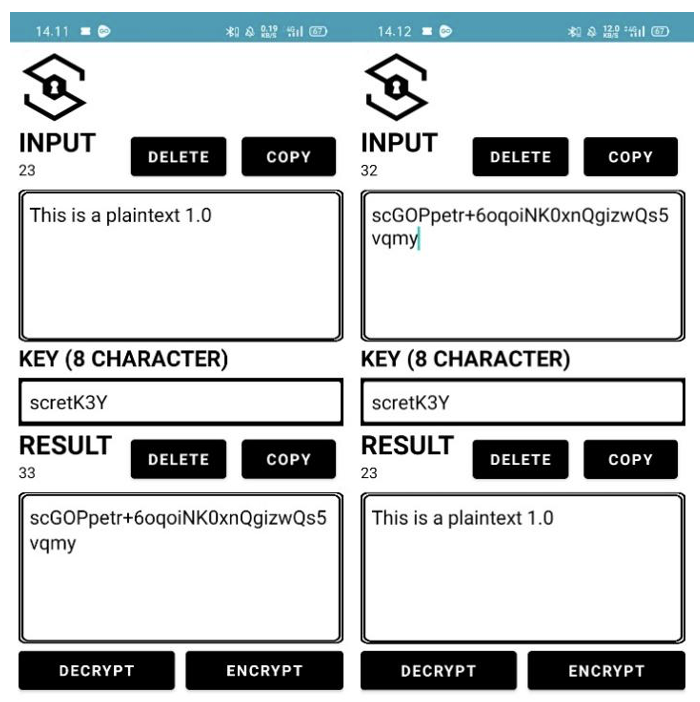
The development of the internet facilitates public communication in sharing information. Along with the advancement of technology in the communication segment, there were various threats to it. Many applications had sophisticated security systems, but the actions in exploiting these security systems were also increasingly diverse. This study implemented a combination of classic and modern algorithms, namely autokey cipher reverse key and DES to protect data from these crimes. This research develops encryption and decryption applications using the agile method, the technique used because of the time spent on the built progress of applications with a cycle for the development process. With this cycle utilized, the method was suitable for developing applications in the short term and revising or improving applications in each cycle. The research resulted in security applications having the function of helping people secure data so that they could prevent and complicate digital criminal acts.
References
and P. J. S. Benckendorff, Pierre J., Zheng Xiang, Tourism information technology. Cabi, 2019.
P. Daponte, L. De Vito, F. Picariello, and M. Riccio, “State of the art and future developments of measurement applications on smartphones,” Measurement, vol. 46, no. 9, pp. 3291–3307, Nov. 2013, doi: 10.1016/j.measurement.2013.05.006.
S. Herring, Culture, technology, communication: Towards an intercultural global village. Suny Press, 2001.
A. Holzinger, P. Treitler, and W. Slany, “Making Apps Useable on Multiple Different Mobile Platforms: On Interoperability for Business Application Development on Smartphones,” 2012, pp. 176–189. doi: 10.1007/978-3-642-32498-7_14.
C. L. Ventola, “Mobile devices and apps for health care professionals: uses and benefits.,” P T, vol. 39, no. 5, pp. 356–364, May 2014.
Y. Y. Lee and C. L. Gan, “Applications of SOR and para-social interactions (PSI) towards impulse buying: the Malaysian perspective,” J. Mark. Anal., vol. 8, no. 2, pp. 85–98, Jun. 2020, doi: 10.1057/s41270-020-00077-5.
J. R. C. Nurse, “Cybercrime and You: How Criminals Attack and the Human Factors That They Seek to Exploit,” in The Oxford Handbook of Cyberpsychology, A. Attrill-Smith, C. Fullwood, M. Keep, and D. J. Kuss, Eds., Oxford University Press, 2019, pp. 662–690. doi: 10.1093/oxfordhb/9780198812746.013.35.
L. Y. Connolly and D. S. Wall, “The rise of crypto-ransomware in a changing cybercrime landscape: Taxonomising countermeasures,” Comput. Secur., vol. 87, p. 101568, Nov. 2019, doi: 10.1016/j.cose.2019.101568.
A. K. Mandal, C. Parakash, and A. Tiwari, “Performance evaluation of cryptographic algorithms: DES and AES,” in 2012 IEEE Students’ Conference on Electrical, Electronics and Computer Science, IEEE, Mar. 2012, pp. 1–5. doi: 10.1109/SCEECS.2012.6184991.
D. Buhalis and P. O’Connor, “Information Communication Technology Revolutionizing Tourism,” Tour. Recreat. Res., vol. 30, no. 3, pp. 7–16, Jan. 2005, doi: 10.1080/02508281.2005.11081482.
S. G. Qureshi and S. K. Shandilya, “Advances in Cyber Security Paradigm: A Review,” 2021, pp. 268–276. doi: 10.1007/978-3-030-49336-3_27.
S. C. Moser, “Communicating climate change: history, challenges, process and future directions,” WIREs Clim. Chang., vol. 1, no. 1, pp. 31–53, Jan. 2010, doi: 10.1002/wcc.11.
R. E. Klima and N. P. Sigmon, Cryptology: Classical and Modern with Maplets. 2012. doi: 10.1201/b12269.
A. M. No Froomkin, Metaphor is the key: cryptography, the clipper chip, and the constitution, 143rd ed. U. Pa. L., 1994.
G. Singh and S. Supriya, “A Study of Encryption Algorithms (RSA, DES, 3DES and AES) for Information Security,” Int. J. Comput. Appl., vol. 67, no. 19, pp. 33–38, Apr. 2013, doi: 10.5120/11507-7224.
K. T. Smith, A. Jones, L. Johnson, and L. M. Smith, “Examination of cybercrime and its effects on corporate stock value,” J. Information, Commun. Ethics Soc., vol. 17, no. 1, pp. 42–60, Jan. 2019, doi: 10.1108/JICES-02-2018-0010.
and M. A. D. Syed Nisar Bukhari, Ashaq Hussain Dar, “Review and analysis of applying agile methodology in software development,” Int. J. Sci. Tech. Adv., vol. 2, no. 4, pp. 187–190, 2016.
M. STOICA, M. MIRCEA, and B. GHILIC-MICU, “Software Development: Agile vs. Traditional,” Inform. Econ., vol. 17, no. 4/2013, pp. 64–76, Dec. 2013, doi: 10.12948/issn14531305/17.4.2013.06.
I. G. Stamelos and P. Sfetsos, Agile software development quality assurance. 2007. doi: 10.4018/978-1-59904-216-9.
Downloads
Published
Issue
Section
License
Copyright (c) 2023 Risandio Ilham Lazuardi, Nuril Anwar

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Start from 2019 issues, authors who publish with JURNAL MOBILE AND FORENSICS agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License (CC BY-SA 4.0) that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work.

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.